只检查 OpenClaw 实例本身
它盯的是本地实例的配置基线、权限边界、暴露面和漂移信号,不去扫外部目标。

它盯的是本地实例的配置基线、权限边界、暴露面和漂移信号,不去扫外部目标。
It stays on local baseline settings, permission boundaries, risky exposure, and drift signals on the instance itself. It does not go looking at the outside world.
运行方式是本地只读,不需要外部 API,也不把本地配置内容传出主机。
It runs locally, read-only, requires no remote API, and does not upload local configuration content off-host.
它不是网络扫描器,不是 IDS,也不是假装什么都覆盖的 all-in-one 平台。
It is not a network scanner, not an IDS, and not another fake all-in-one platform.
Lite 负责把问题讲清楚。修正、备份、回退准备和更深的处置,留给 M78Armor Core。
Lite is there to make the problem clear. Fixes, backup, rollback readiness, and the steadier remediation path stay in M78Armor Core.
检查网关绑定地址、默认端口使用情况,以及是否把本应本地优先的实例暴露得过宽。
Checks gateway bind scope, default-port usage, and whether a local-first instance is exposed more broadly than it should be.
检查认证令牌是否缺失或过弱,配置中是否存在明文密钥和其他弱默认值。
Checks whether authentication tokens are missing or weak, and whether plaintext secrets or other weak defaults still remain.
检查沙箱模式、工作区隔离和高权限工具开关,避免把实例变成过度开放的执行面。
Checks sandbox mode, workspace isolation, and elevated-tool settings so the instance does not turn into an unnecessarily open execution surface.
检查浏览器私网访问、CDP 来源范围、Control UI 来源允许列表,以及其他控制面边界。
Checks private-network browser reach, CDP source range, Control UI origin allowlisting, and other control-plane boundaries.
检查 TLS 配置与日志级别,避免在更广暴露面下继续泄露过多上下文或走弱传输路径。
Checks TLS settings and log verbosity so wider exposure does not continue to leak unnecessary context or weaker transport handling.
检查插件迁移状态和允许列表是否仍处于宽松或遗留状态,减少插件边界漂移。
Checks whether plugin migration state and allowlisting remain weak or legacy-driven, reducing plugin-boundary drift.
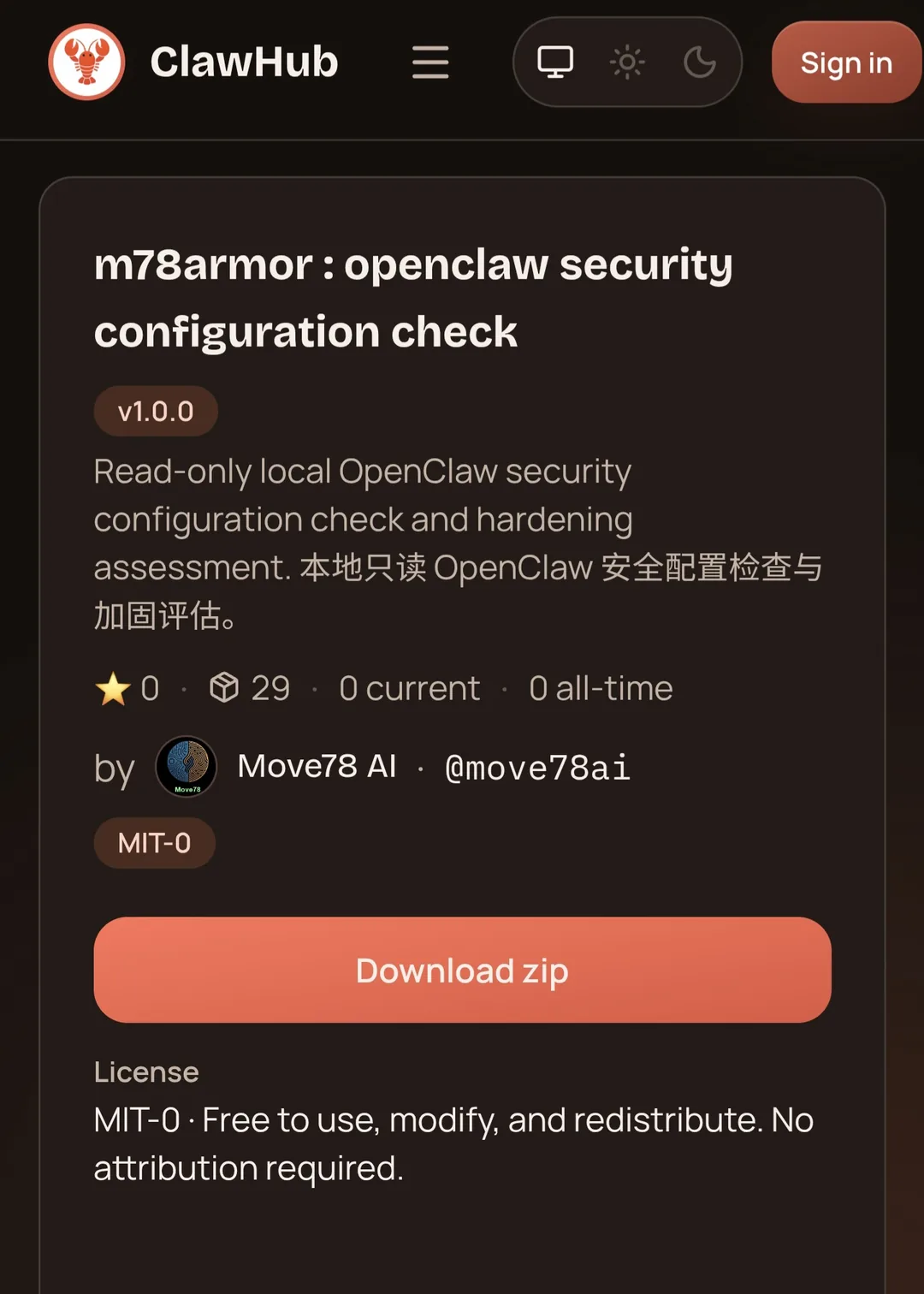
运行 m78armor : openclaw security configuration check 检查这个 OpenClaw 实例的安全配置问题 执行本地 OpenClaw 配置基线与加固评估
run m78armor : openclaw security configuration check check this openclaw instance for risky security configuration gaps review local openclaw configuration baseline and hardening issues
node ./scripts/m78armor-lite.js --lang zh node ./scripts/m78armor-lite.js --json node ./scripts/m78armor-lite.js --config "/path/to/openclaw.json" --lang zh
node ./scripts/m78armor-lite.js --lang en node ./scripts/m78armor-lite.js --json node ./scripts/m78armor-lite.js --config "/path/to/openclaw.json" --lang en
| 能力 | M78ARMOR-LITE | M78ARMOR CORE |
|---|---|---|
| 角色 | 安装后本地只读检查 | 本地执行、加固与后续控制 |
| 配置发现 | 有 | 有 |
| 自动修正 | 无 | 有 |
| 变更前备份 | 无 | 有 |
| 回滚 | 无 | 有 |
| 更深层风险检查 | 有限 | 更深 |
| 输出 | 人类可读 + 最小 JSON | 更丰富、可追踪 |
| Capability | M78ARMOR-LITE | M78ARMOR CORE |
|---|---|---|
| Role | Post-install local read-only check | Local execution, hardening, and safer follow-through |
| Configuration findings | Yes | Yes |
| Automatic remediation | No | Yes |
| Backup before change | No | Yes |
| Rollback | No | Yes |
| Deeper risk-aware checks | Limited | Deeper |
| Output | Human-readable + minimal JSON | Richer and more traceable |
Lite makes the problem clear. Core handles backup first, then fixes, with rollback when needed. You are not buying another report. You are buying the steadier way to finish the work.
See Core fixes and rollback